쪽팔리면 질문하지 맙시다. 소중한 답변 댓글을 삭제하는건 부끄러운 일 입니다
안녕하세요
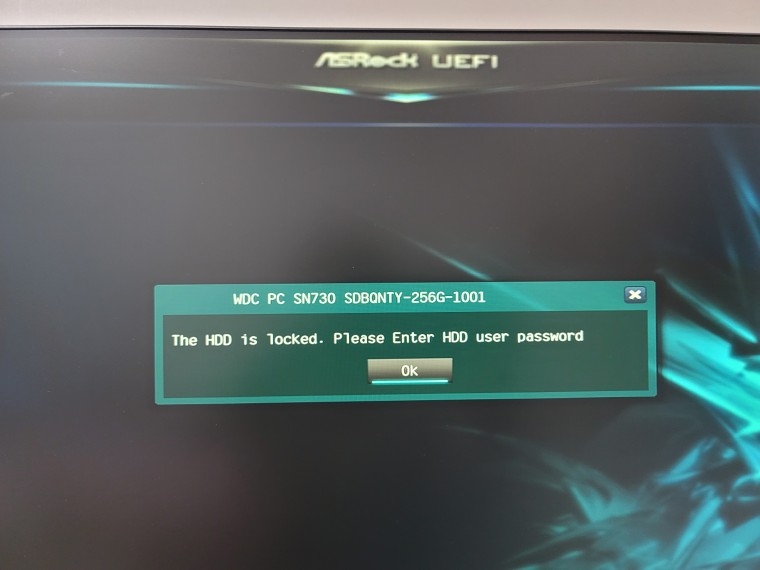
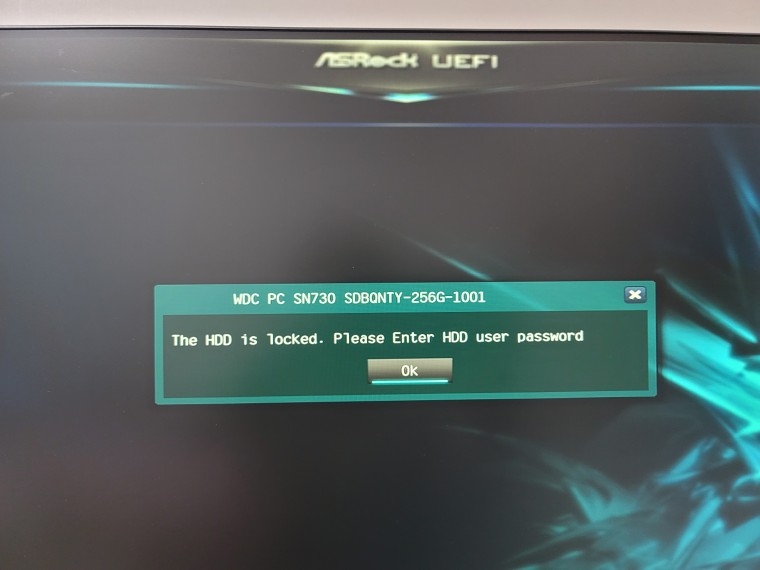
얼마전에 시모스 설정하다가
호기심에 ssd 비번 거는게있어서
걸었다가... 비번을 까먹었습니다.....
시모스 초기화해도 안되고...
수입사인 d*d컴에 문의해도 어쩔수 없다는 답변만 받았는데 혹시나 방법이 있을까해서 여쭤봅니다
감사합니다!!@
쪽팔리면 질문하지 맙시다. 소중한 답변 댓글을 삭제하는건 부끄러운 일 입니다
안녕하세요
얼마전에 시모스 설정하다가
호기심에 ssd 비번 거는게있어서
걸었다가... 비번을 까먹었습니다.....
시모스 초기화해도 안되고...
수입사인 d*d컴에 문의해도 어쩔수 없다는 답변만 받았는데 혹시나 방법이 있을까해서 여쭤봅니다
감사합니다!!@
�����ʱ�ȭ �� �ȴٸ�...
�װ��� ���� �ɰ� ����
PSID ��ȣ�� SSD ��ƼĿ�� �����ֽ��ϴ�.
BIOS���� HDD�� �Ŵ� ��й�ȣ�� HDD/SSD ��Ʈ�ѷ����� �Ŵ°Ŷ� ���κ��� �ʱ�ȭ�� �ǹ� �����ϴ�.
��� �����մϴ� (__)
Western Digital PC SN730 NVMe SSD supports sanitization of user data using the
Format NVM command in one of the following modes:
1. The No Secure Erase mode implements logical erase of user data: cleanup of FTL
tables marks all blocks as unallocated. Subsequent read commands return zeroes
for erased data.
2. The User Data Erase mode implements physical erase of user data with NAND
block erase operation. The process covers all user LBAs including any spare and
re-allocated blocks.
3. The Crypto Erase implements cryptographic erase of user data by eradicating its
encryption key. The Crypto Erase mode is not supported on Non-SED devices.
Western Digital PC SN730 NVMe SSD SED supports sanitization of user data using the
Sanitize command in one of the following modes: Block Erase and Crypto Erase. The
Overwrite mode is not supported.
Sanitization of locked devices is supported on PC SN730 NVME SSD SED with PSID
revert command.
Table 8-1 summarizes sanitization modes and their result:
Table 8-1. Western Digital PC SN730 NVMe SSD Format NVM Modes and Results
8.3 Security of Read-Only Mode
Device enters Read-Only mode upon reaching End-of-Life conditions for user media.
In this mode, it stops accepting commands that might write user or system data.
Format NVM in the User Data Erase and the Crypto Erase mode is also supported
when device turns read only mode. It provides a secure option to erase all user data
before disposal of the device or before returning it for FA. Successful status returned
for the command is an indication of complete sanitization of user data. If device fails
to complete the process, sanitization should be addressed by physical destroy
methods, e.g. shredding.
Device preserves TCG locking settings as configured before transition to Read-Only
mode. Host application shall be ready that NVMe commands Format NVM and Sanitize
are aborted when device is Write-locked. Host shall unlock device with valid user
password before applying the command. Alternatively, it shall use sanitization
commands of the active TCG Opal protocol: TCG Revert.
PC SN730 NVMe SSD, Non-SED
Command Mode Operations Data at Rest Read Result
Format NVM 000b (No Secured Erase) FTL Cleanup Last Written Zeros
001b (User Data Erase) FTL Cleanup,
Block Erase
Erased Zeros
010b (Crypto Erase) N/A N/A N/A